Andy Yen stood in the hum of CERN’s labs, ideas and data flying between scientists from more than a hundred countries. Email wasn’t just messages – it kept projects moving and careers tied together. He saw the risk hidden in plain sight: every message left a trail that could expose sensitive research to the wrong people. Years studying physics at Caltech and Harvard trained him to spot patterns others missed. Now the pattern looked like a trust problem disguised as a tech issue.
He grew up across continents, so privacy felt personal, not academic. Crossing borders teaches that small details can carry big consequences. The Snowden leaks landed hard, showing that trusted email providers might hand over private details without users ever hearing about it. At CERN, a culture of openness sat next to fierce independence. Those values didn’t always fit with the surveillance reality he was seeing.
Hallway conversations with cryptographers pushed a simple truth to the front: privacy that adds hassle won’t last. If a tool slows teamwork, people drop it. Protection needs to live inside everyday tools and feel invisible – no complicated setups, no special steps, just private communication that works at the speed of research.
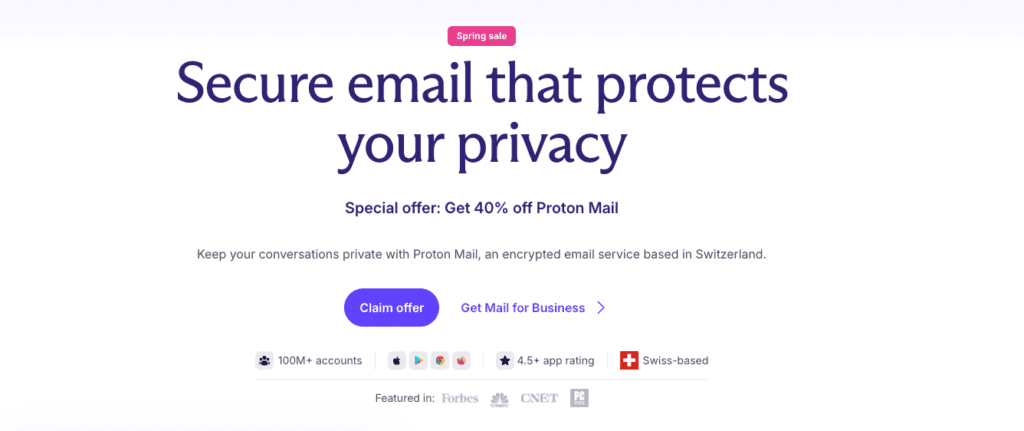
How a research problem at CERN became ProtonMail’s product bet
In 2013, Andy Yen and a small team, including Jason Stockman and Wei Sun, started sketching a simpler way to keep email private. Encryption would run in the browser before a message ever left the device. Servers would never see plaintext, so even ProtonMail couldn’t read stored mail. Client-side key generation and storage meant no single master key existed for anyone else to take.
The first version had clear targets. People could send and receive encrypted mail inside ProtonMail, protect subject lines, and send password-locked messages to outside contacts. That last piece mattered. It showed a push for privacy that didn’t force everyone into messy key exchanges or old-school PGP habits. They stayed close to OpenPGP so it still worked with familiar tools, but they pushed hard on usability.
Switzerland became home for a practical reason, not scenery. Strong privacy laws and political neutrality offered better legal cover. Hosting there set strict rules for the product. No plaintext on servers. Not contacts, not bodies of emails. Search lived on the client. Even simple features needed careful design around these constraints. Account recovery was a headache. Lose keys, lose access. Education had to sit next to product work, while they tested encrypted recovery paths.
Some choices came with real trade-offs.
- Web crypto in 2013 was raw. Picking between SJCL, OpenPGP.js, or waiting on the WebCrypto API slowed decisions.
- Swiss jurisdiction boosted trust, yet added operational complexity.
- Zero-access servers blocked server-side search and a few other comforts, but preserved privacy where it counted.
Crowdfunding proved demand and shaped ProtonMail’s early scope
Public support for private email didn’t look hypothetical in 2014. It looked like real people pulling out their wallets fast. ProtonMail’s Indiegogo campaign surged past expectations, with more than $500,000 from nearly 10,000 backers in a few days. The signal was hard to miss: privacy had demand, and people were ready to pay for it.
The campaign did more than raise money. It funded core infrastructure – Swiss data centers aren’t cheap – and doubled as a market test. Would users pay for privacy and stay long enough to shape the product? Early backers got perks like extra storage and custom domains. Those incentives revealed which features mattered most beyond a free plan.
Trust grew through open, straightforward updates. The team explained encryption choices in detail and even shared photos of server sites in Switzerland. These specifics cut through doubts about opaque “black box” systems and helped backers feel part of something concrete.
Backer questions became a steady feedback loop. Onboarding snags showed up fast: encryption key management, account recovery, and emailing people outside ProtonMail caused friction. Those issues pushed redesigns that reduced early hurdles and clarified tough steps.
Success created new pressure. Waitlists swelled into the hundreds of thousands as word spread, but scaling too fast risked slowdowns and delivery glitches. Invites rolled out in controlled waves to keep performance steady while growth continued.
Funds went to immediate needs. Swiss data center costs topped the list, with DDoS protection and thorough code audits close behind. Hiring accelerated for cryptography specialists and frontend developers who could turn complex security work into straightforward experiences.
The outcome wasn’t just a big fundraising total. It proved a point: when privacy tools are explained clearly and backed by earned trust, people will pay to support them.
Building privacy‑first email that still works with the email ecosystem
Building a privacy-first email service meant constantly balancing strong security with a familiar inbox experience. ProtonMail’s zero-access design handled the hard part. Message bodies and attachments get encrypted on the user’s device with session keys, and those keys get wrapped with recipients’ public keys before anything leaves the browser. Servers never see plaintext. Not even ProtonMail.
Search created a real dilemma. Server-side search would expose content, so the team went with client-side search and encrypted local indexes. It runs slower than traditional services, but it also keeps messages protected.
Passwords did more than unlock an account. Authentication split into two steps, with one password for login and another to decrypt the mailbox. The model changed over time to reduce friction while keeping strong protection.
Sending secure emails to people outside ProtonMail needed a practical path. Password-protected messages used shared secrets or expiring links so non-Proton recipients could read them without complicated key exchanges. It preserved end-to-end encryption goals and stayed usable for real conversations.
Spam filtering brought different trade-offs. Content scanning wasn’t available, so server-side heuristics focused on metadata like sender reputation and sending patterns. Rate limits and reputation systems carried most of the weight, keeping abuse down without opening messages.
Email deliverability required careful tuning. DKIM, SPF, and DMARC proved sender legitimacy, while tight DNS record management avoided leaking details about users or infrastructure during growth.
Mobile apps pushed security further with native cryptographic libraries and hardware-backed key storage such as secure enclave or keychain. Private keys stayed protected even if a device was compromised.
Supply chain risks got direct attention. Reproducible builds tied shipped apps to audited source, and regular third-party reviews of cryptographic libraries caught flaws early.
Key architectural features:
- Zero-access encryption keeps plaintext off servers by encrypting data on the client before transmission.
- Client-side inbox search trades speed for privacy with encrypted local indexes.
- Dual-password design separates login from mailbox decryption, with UX updates that reduced friction over time.
- Password-protected external emails use shared secrets or expiring links for secure delivery beyond ProtonMail without complex key exchange.
- Spam prevention uses metadata-based heuristics, reputation, and rate limits instead of content inspection.
- Mobile app security uses platform-native crypto and hardware-backed key storage to lower exposure risk.
Why trust is a product feature for privacy startups
Trust isn’t a slogan for ProtonMail. It guides decisions. They published a clear threat model early, named the likely adversaries – criminals, advertisers, state actors – and drew a firm line on what the service defends and what it can’t. Honest limits set real expectations.
Opening core code to public review backed that up. By open-sourcing cryptographic libraries and client apps, they asked independent experts to inspect, break, and improve the work. It’s a hard test that catches issues sooner and builds confidence.
Swiss law adds strong legal safeguards. Hosting key systems in Switzerland forces any request through Swiss courts, which set a high standard. End-to-end encryption keeps message content unreadable even if data gets handed over, while only limited metadata may be exposed under strict rulings.
Security practice matched the architecture. Bug bounty programs paid ethical hackers to report flaws. Independent audits reviewed cryptography and application layers to spot problems before they turned into news.
Their transparency covered data practices, not just code. ProtonMail collects minimal IP logs by default and offers Tor access for people who need extra cover to lower traceability. They publish transparency reports that show how many legal requests arrived, how they were processed, and the outcomes – without revealing sensitive operations.
Growth choices avoided invasive analytics and tracking profiles. Opt-in, anonymous aggregate telemetry gave enough feedback to improve reliability while respecting privacy.
Public cases involving law-enforcement requests became lessons for users. These moments showed where privacy protections stay solid and where legal reach imposes limits, depending on jurisdiction.
Adversaries in the threat model include:
- Criminals seeking financial gain or disruption
- Advertisers trying to harvest data for targeting
- State actors pursuing surveillance or control
Transparency efforts include:
- Regular transparency reports detailing legal demands and responses
- Open-source releases for community audits and contributions
- Bug bounty programs that reward proactive vulnerability discovery
These steps point to a simple idea: trust grows with accountability, not secrecy.
Scaling ProtonMail without breaking reliability or deliverability
ProtonMail’s early launch drew far more people than the system could handle. Waitlists grew fast, so the team scaled in steps. They set up peering and added multiple MX records to spread mail traffic. Anycast routing helped absorb DDoS pressure and kept the service steady under strain.
They first added multi‑region redundancy inside Switzerland, then across Europe. Traffic shifted around outages and slow patches without breaking the user experience. Reliability rose to meet higher expectations.
Inside the platform, message queues controlled bursts of work. Backpressure stopped a busy component from slowing everything else. Key lookups and crypto workers stayed protected when usage spiked. Throttling reduced the risk of cascading failures during peak hours.
Abuse controls matured in parallel. Automated vetting flagged risky sign‑ups early. CAPTCHAs were tuned to avoid leaking personal data, balancing safety with privacy. Creation‑rate monitoring exposed disposable email abuse before it spread.
Customer support had to adapt to rising volume. Triage used in‑app tips and a searchable help center to answer common questions fast. Paid users received priority channels, which sped up responses without overwhelming the queue.
Email deliverability got careful attention. Agreements with large mailbox providers reduced spam false positives. Feedback loops informed constant adjustments. IP warming brought new sending ranges into trusted status in gradual steps.
Costs stayed under control by design. Commodity hardware backed encrypted storage, with erasure coding protecting data integrity without expensive vendor stacks or cloud lock‑in. In‑house tools replaced costly third‑party software to keep operations lean and reliable.
User growth surged by an order of magnitude month over month during peak times. Trust shaped conversions from free to paid, funding continued expansion without ad spend.

From ProtonMail to Proton, expanding a privacy‑by‑default suite
Proton didn’t stop at email. The team knew privacy had to cover more than messages, so they launched ProtonVPN to protect internet traffic from snoops. This wasn’t about stacking products. It expanded the promise of privacy across daily life. Shared account systems and common security standards linked ProtonMail and ProtonVPN, so trust in one carried over to the other.
Next came Drive and Calendar, built with end-to-end encryption at the core. Files in Proton Drive stayed encrypted with keys on user devices, and events in Proton Calendar followed the same strict model. The key flows looked and felt the same across apps, which made tough crypto steps feel simple. The goal wasn’t just to lock data, but to do it without turning people into cryptographers.
A single Proton Account pulled everything together, from sign-ins to recovery. One subscription, Proton Unlimited, bundled the apps and increased average revenue per user, all while staying on mission. No ads, no data sales, just privacy paid for by people who want it. Pricing tiers kept a free option available and funded ongoing work.
Business users weren’t left out. Custom domains and multi-user admin tools gave small teams and larger orgs private communication without breaking core promises around confidentiality. This B2B focus added revenue and stayed true to the same principles that built user trust early on.
Design consistency mattered more than it might seem. A shared look and familiar onboarding made adding a second or third Proton app feel natural, not jarring. Less friction meant lower acquisition costs as people moved across the suite.
Proton shifted from a single app to a connected set of privacy tools. Confidence in one service sparked interest in the next, creating a network effect driven by trust, not gimmicks or tracking.
- Key expansions include:
• Launch of ProtonVPN for encrypted internet traffic protection
• Introduction of Proton Drive (encrypted file storage) and Calendar (secure scheduling)
• Unified account system with bundled subscriptions enhancing revenue models
• Enterprise features supporting business needs without compromising privacy
Real‑world security trade‑offs with phishing, passwords, and recovery
Phishing keeps slipping past defenses, so ProtonMail raised the bar on logins. Support for WebAuthn and FIDO2 brings hardware keys and biometrics that resist tricks far better than passwords. Sign-in stays quick while attack windows shrink.
Inside the inbox, clear warnings flag mail from unfamiliar senders or lookalike domains. These prompts encourage a quick check before clicking links or sharing data. Simple key verification cues confirm when a message is truly secure, turning routine checks into small security wins.
Passwords once felt awkward, with one for the account and another to unlock the mailbox. ProtonMail moved to a cleaner model that pairs strong hashing like Argon2 with optional two-factor authentication. Security holds firm while friction drops.
Account recovery got extra care. Encrypted recovery keys protect mailbox content during resets. Optional recovery emails avoid exposing sensitive details, so fixes don’t chip away at privacy.
Proton Drive shares rely on short-lived keys that expire fast, limiting damage if a link spreads. The interface also nudges people away from putting secrets in email subjects since those aren’t end-to-end encrypted. Small cue, big protection.
Abuse response teams scan for unusual login patterns that suggest credential stuffing. They do this without keeping personal fingerprints, preserving privacy while staying alert.
When new scams show up, like MFA fatigue attacks, the team turns them into timely lessons through newsletters and in-product tips. Guidance appears where it’s needed, not buried in long manuals.
Regular red team drills mimic phishing breaches so responders spot and contain threats faster over time. Practice keeps defenses sharp without piling complexity on users.
Practical lessons for building a durable privacy startup
Clear goals guided every move from day one. ProtonMail treated “privacy by default” as a hard rule, not a slogan. Picking Switzerland wasn’t about scenery, but matched the legal safeguards they needed. Passing on ad money kept users first, avoiding short-term gains that would weaken trust.
Trust took time and grew step by step. Transparency reports showed how data requests were handled. Regular audits and open-source code welcomed scrutiny instead of hiding anything. This steady openness built real brand strength. When new products launched later, adoption came easier because people already believed in the team’s integrity.
Security goes beyond locks and walls. Usability protects people too. Extra steps and confusing prompts drive users away, even those who care about privacy. Strong encryption that runs quietly keeps email smooth. Friction shows up only when risk spikes, like during password resets or flagged logins.
Acknowledging limitations earns respect from technical users. End-to-end encryption blocks some server-side features. Inbox search is a common example. Framing this as a deliberate trade-off, not a failure, builds credibility with people who understand how the tech works.
Crowdfunding gave early momentum and public accountability at the same time. Backers wanted frequent, technical updates over vague promises. That rhythm created a tight feedback loop, sharpened priorities, and kept supporters engaged through rough patches.
Laws shape systems. Model the legal environment like any other hard dependency and plan for worst cases. Swiss jurisdiction became part of both architecture and policy, so pressure wouldn’t force compromises on core principles.
Slow, steady scaling beats explosive growth when privacy is at stake. Protect deliverability, uptime, and support capacity during spikes. Lose those and trust slips fast, in ways no campaign fixes later.
Diversified, aligned revenue pays for free tiers without ads or data sales. That keeps the business healthy and confidence high.
Top lessons at a glance:
- Mission-led choices anchor long-term strategy beyond trends
- Transparency compounds trust and lowers future acquisition costs
- Easy, thoughtful usability strengthens security by reducing barriers
- Clear, direct communication about limits builds loyal power-user communities
- Careful scaling preserves reputation during rapid growth
What CERN and Proton teach today’s founders about earning trust
Andy Yen went from particle physics at CERN to building ProtonMail, and the path offers sharp lessons for anyone shipping privacy-first tools today. Start by knowing who the attacker is. Map a simple threat model, like a scientist writing down sources of error. Spell out adversaries, likely attack paths, and failure points. That clarity shapes product choices and keeps security practical.
Trust has to live in the product, not the marketing. ProtonMail’s zero-access design forced hard calls, and the team said so in plain terms. Slower search at times. Metadata-based spam filters. Limits that exist for a reason. Open source and public audits helped prove claims instead of asking for blind faith. Honesty bought credibility.
Place matters. Operating in Switzerland wasn’t set dressing. Local law set boundaries for data requests and gave Proton leverage when it mattered. A supportive jurisdiction protects users and the team, and it influences architecture from the start.
Growth stayed deliberate. Waitlists, careful rollouts, then redundancy across regions. Reliability counted as growth because uptime builds reputation, and reputation keeps users. Moving slower on purpose avoided brittle systems and noisy incidents.
Practical next steps for builders: write a one-page threat model this week with key risks and non-negotiables. Post it publicly to invite scrutiny and set expectations. Pick one point in the main user flow where friction feels high, remove it without weakening security, then ship the change and study outcomes.
These lessons came from lab benches, crowdfunding, and years of shipping encrypted email, then VPN, Drive, and Calendar with the same end-to-end mindset. Real trade-offs, documented and defended, turned into long-term trust.
What trade-offs sit in your roadmap? How will trust grow month after month? Share experiences to help others working through the same problems.
Leave a Reply